August 13, 2021 by Admin
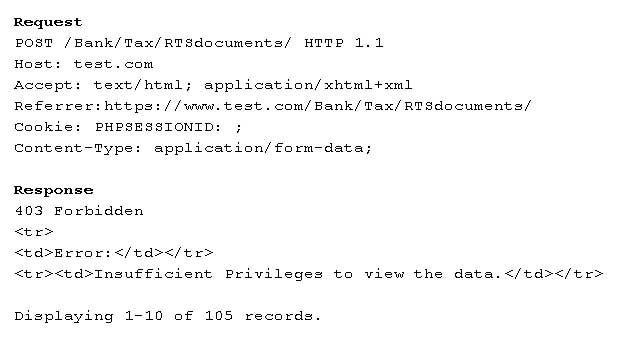
A penetration tester is testing a banking application and uncovers a vulnerability. The tester is logged in as a non-privileged user who should have no access to any data. Given the data below from the web interception proxy:
Which of the following types of vulnerabilities is being exploited?
- Forced browsing vulnerability
- Parameter pollution vulnerability
- File upload vulnerability
- Cookie enumeration